How Exclaimer delivers reliability and security at scale
10 February 2026
0 min read
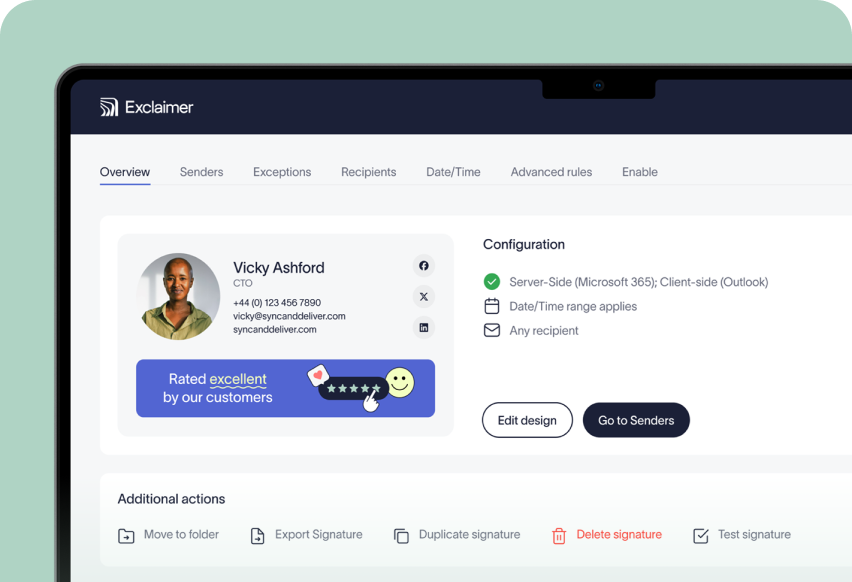
Every email your organization sends reflects your brand, carries legal weight, and needs to be consistent. At scale, that means your email signature management tool has to be reliable, secure, and built for enterprise complexity.
Exclaimer applies signatures automatically and consistently across Microsoft 365 and Google Workspace. To do that without introducing risk, it’s built for stability, transparency, and secure operation from the ground up.
This article outlines how Exclaimer handles reliability and security. You’ll see how the service is built, how data is processed, and what controls support governance, compliance, and operational continuity.
It'll cover:
How Exclaimer applies signatures without storing email content
Where data is hosted and how data residency is maintained
How encryption, access control, and system isolation are handled
Which certifications and audits verify our security posture
How we maintain high availability and recover from outages
By the end, you’ll find it easier to assess Exclaimer and understand how it fits into your wider digital communications governance and compliance strategy.
Exclaimer reliability and security at a glance
Here’s a quick look at how Exclaimer handles reliability and security.
No email content is stored. Emails are processed in transit to apply the correct signature, then delivered.
Built on Microsoft Azure. All processing happens in regional datacenters to meet data residency needs.
In-region data handling. Customer data stays local to support compliance with GDPR, CCPA, HIPAA, and similar regulations.
End-to-end encryption. Data is encrypted in transit and at rest using standard protocols.
Independently certified. Exclaimer holds SOC 2 Type II, ISO 27001, and ISO 27018 certifications.
Engineered for uptime. Active-active infrastructure and automatic failover keep services running.
Proven reliability. Exclaimer delivers 99.99% uptime, backed by full monitoring and system redundancy.
These controls help IT teams maintain governance, compliance, and stability—without adding complexity or creating risk in your email environment.
To see all of our security accreditations, visit the Exclaimer Trust Center. It includes summaries, certificates, reports, policy documents, and answers to over 350 security and compliance questions.
Does Exclaimer store email content?
No. Exclaimer doesn’t store or retain email content. Emails pass through Exclaimer briefly so the correct signature can be applied. Once stamped, the message returns to the mail flow. No content is stored, archived, or accessible to Exclaimer.
This design’s intentional. It limits risk, reduces exposure, and avoids creating a second system of record.
How email processing works
When an email is sent, Exclaimer:
Checks which signature applies
Adds the signature to the message
Immediately returns the email to the mail flow
At no point does Exclaimer store message content, attachments, or conversation history.
What data is retained, and why
To support performance and troubleshooting, Exclaimer logs limited metadata for a short time:
Sender and recipient addresses
Signature ID applied
This doesn’t include content, subject lines, or attachments. Metadata is automatically purged after a short retention window.
Why this matters for IT and security
Processing emails in memory, with no content retention, means:
Lower risk in the event of a breach
Smaller compliance scope
No additional data repository
Alignment with GDPR and other data minimization requirements
For IT and security teams, this approach provides centralized signature control without expanding the attack surface.
How Exclaimer is built on Microsoft Azure for reliability and scale
Exclaimer runs entirely on Microsoft Azure. Its architecture uses regional, high-availability infrastructure to apply signatures without disrupting mail flow.
Azure is a platform widely trusted by IT teams for running mission-critical services. Exclaimer's designed to operate fully within the Microsoft Cloud environment, allowing emails to be processed securely and consistently without leaving Azure’s network.
Optimized for Microsoft Azure from the ground up
Exclaimer’s service is architected specifically for Azure, rather than being retrofitted onto a generic cloud platform.
That design enables:
Regional deployment aligned to customer location
Built-in scalability to handle growth in users and email volume
Consistent performance across global environments
Microsoft Azure’s own compliance framework underpins this infrastructure, supporting regulatory requirements across regions and industries. Exclaimer builds on those controls with additional service-level safeguards.
High availability and uninterrupted mail flow
Email flow reliability is a non-negotiable requirement for IT teams. Exclaimer addresses this with an active-active High Availability Cluster (HAC) model.
When the service is operating normally:
Emails are processed by paired Azure datacenters within the same region
Traffic's distributed using automated load balancing
Each datacenter can handle the full regional load if required
If an issue affects one Azure datacenter, Exclaimer automatically switches processing to the alternate datacenter. This happens without manual intervention and without interrupting email delivery.
Load balancing and fault handling
Exclaimer uses Azure-native load balancing to reduce risk and maintain service continuity.
Key elements include:
Automated traffic distribution across regional datacenters
Continuous synchronization of tenant data within the region
The ability to remove a datacenter from rotation automatically or manually if needed
This approach minimizes single points of failure and supports Exclaimer’s 99.99% service availability target.
Data handling within regional clusters
All data required to operate an Exclaimer subscription is hosted securely in Microsoft Azure.
Data is stored within a High Availability Cluster in the customer’s designated region, which means:
Data residency is maintained by design
Customer data isn't stored outside the assigned geography
Requirements under GDPR, CCPA, and similar regulations are supported
This includes configuration data, signature templates, and directory attributes. Email message content isn't stored as part of this process.
Secure connections and service hardening
All connections to and within the Exclaimer service are secured using SSL certificates and TLS encryption. These connections are continuously monitored to meet current cloud security standards.
Before any updates are deployed:
Changes are built and tested by Exclaimer’s development and QA teams
Services are stress-tested beyond normal usage levels
Code is scanned for malware and verified using native Azure antimalware tools
Updates are rolled out out of hours for each region to minimize operational impact.
Global availability by design
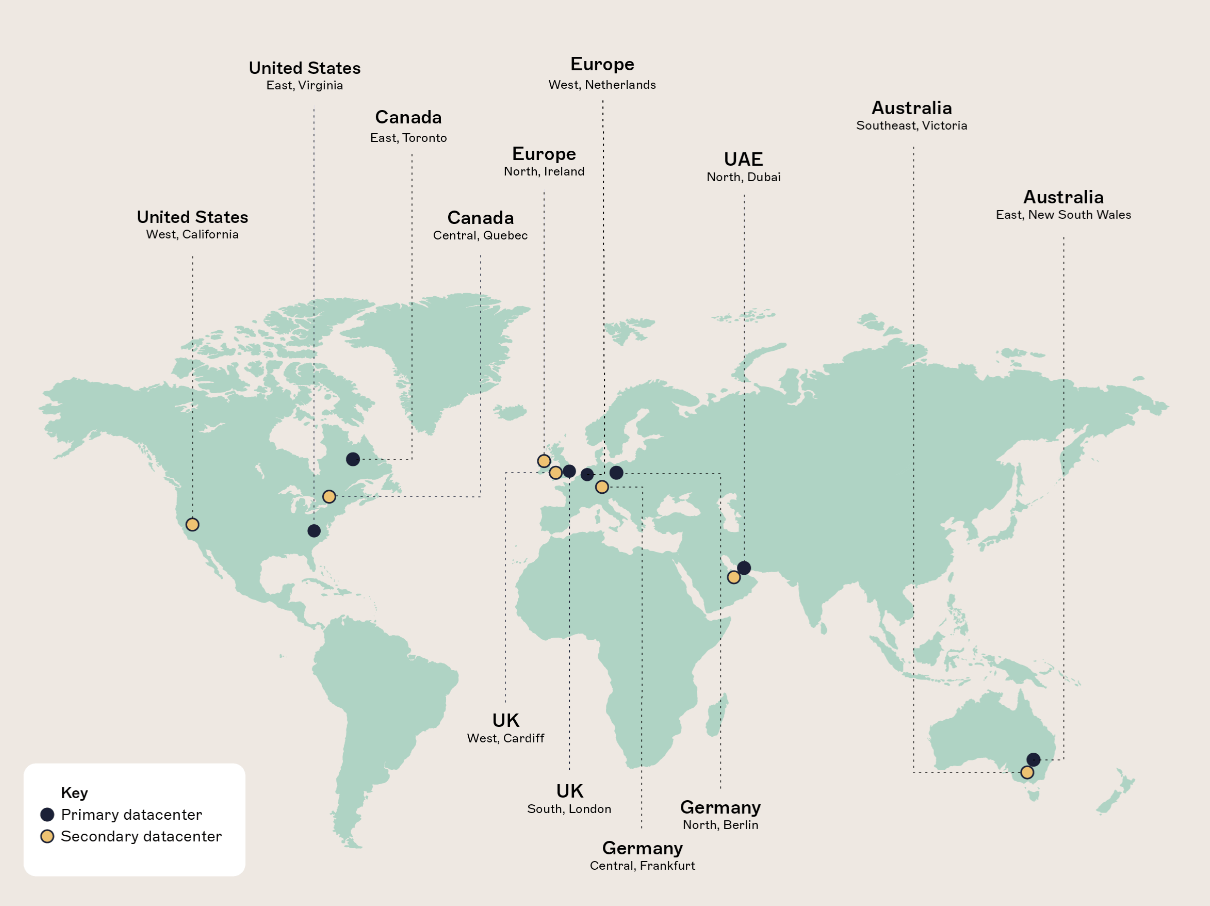
Exclaimer operates across 14 Microsoft Azure datacenters worldwide, arranged in regional pairs.
This global footprint allows Exclaimer to:
Keep customer data within geographic boundaries
Deliver consistent performance across regions
Protect against local Azure infrastructure issues
Each regional datacenter pair is designed so that either location can support the full workload if required, preserving service continuity.
Region | Primary Datacenter | Secondary Datacenter |
|---|---|---|
USA | East US Virginia | West US California |
Canada | Canada Central Quebec | Canada East Toronto |
Europe | West Europe Netherlands | North Europe Ireland |
UK | UK South London | UK West Cardiff |
Germany | Germany W Central Frankfurt | Germany North Berlin |
Australia | Australia East NSW | Australia Southeast Victoria |
Middle East/East Asia | UAE North Dubai | UAE North Dubai |
IT teams can check system status anytime via Exclaimer’s Service Health page, which offers real-time performance and incident updates.
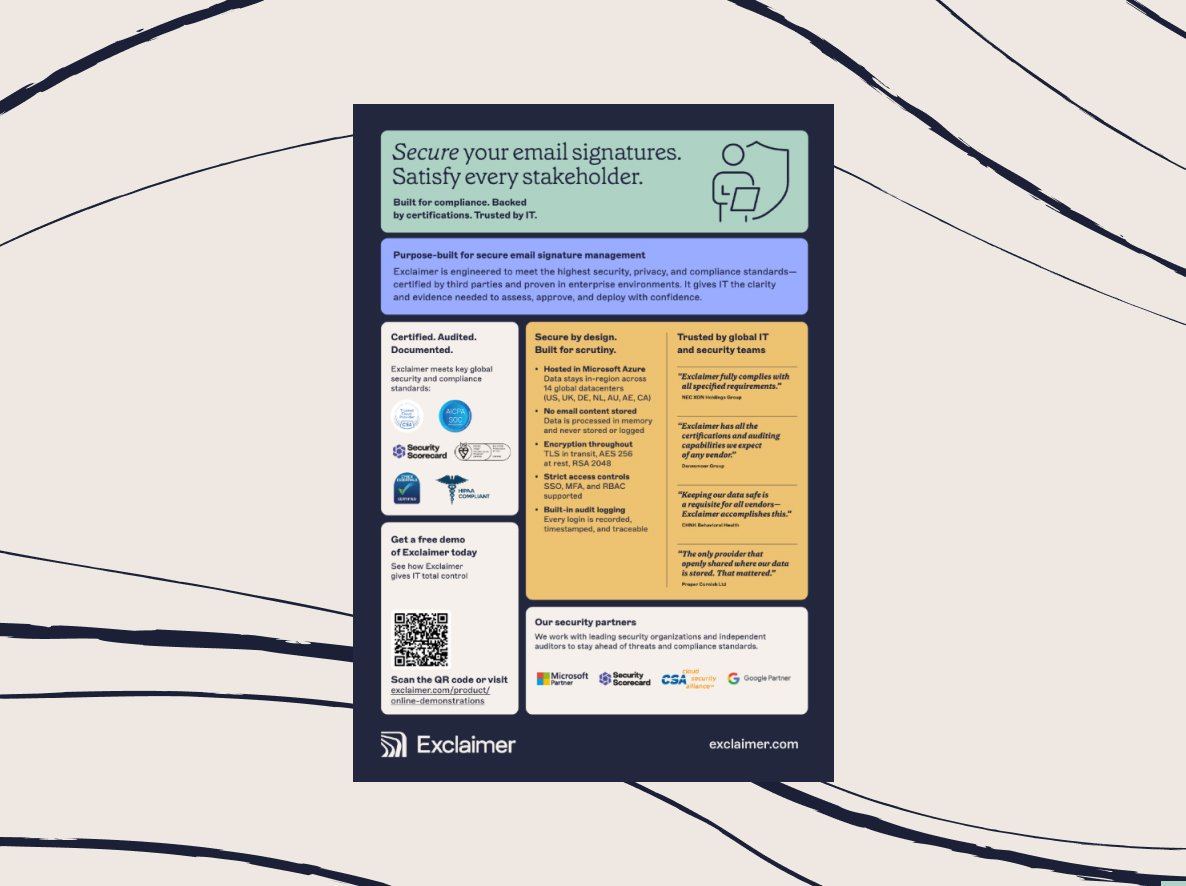
What security certifications and compliance standards does Exclaimer meet?
Exclaimer is independently audited and certified against globally recognized security and privacy standards, including SOC 2 Type II, ISO 27001, ISO 27018, and Microsoft 365 Certification.

These certifications validate how Exclaimer is built, operated, and governed. They provide external assurance that security, availability, confidentiality, and privacy controls are not only defined but consistently followed in practice.
SOC 2 Type II
Exclaimer holds a SOC 2 Type II attestation, confirming that its systems meet the Trust Services Criteria:
Security
Availability
Confidentiality
A SOC 2 Type II report evaluates how controls operate over an extended period rather than at a single point in time. This demonstrates that Exclaimer’s safeguards are not just defined, but consistently applied during day-to-day service delivery.
Within the email signature management category, Exclaimer is currently the only provider publicly attested to SOC 2 Type II. This reflects the level of operational maturity required to meet ongoing audit standards across a global, cloud-based service.
For customers operating under regulated environments (e.g., HIPAA), this attestation provides independent assurance that controls supporting data protection, access management, and service availability are effective.
ISO/IEC 27001
Exclaimer has been certified to ISO/IEC 27001 by the British Standards Institution (BSI) since 2016. This international standard defines how to establish, operate, monitor, and continually improve an Information Security Management System (ISMS) covering people, processes, and technology.
Certification means Exclaimer undergoes regular independent audits to confirm ongoing compliance with internationally accepted security controls.
ISO/IEC 27018
Exclaimer is also certified to ISO/IEC 27018, an extension of ISO 27001 focused on privacy protections for personally identifiable information (PII) in cloud services.
This standard introduces additional controls for:
Secure PII handling
Transparency around data use
Rights related to the use of personal data
ISO 27018’s focus helps ensure that cloud-based processing is aligned with modern privacy expectations.
Microsoft 365 Certification
Exclaimer is a Microsoft 365 Certified application, following a detailed security review and audit conducted by Microsoft.
This certification verifies that:
The application integrates securely with Microsoft 365
Data handling aligns with Microsoft’s security requirements
The service meets Microsoft’s standards for cloud applications
For IT teams operating in Microsoft environments, this provides confidence that Exclaimer's been reviewed and approved within the Microsoft ecosystem.
GDPR and global data privacy regulations
Exclaimer complies fully with the EU General Data Protection Regulation (GDPR) and is regularly audited to confirm ongoing adherence.
For customers in the EU and EEA:
Personal data is processed within European datacenters
Data is hosted in Germany, the Netherlands, and Ireland
No data transfers occur between the UK and EU/EEA environments
Exclaimer also aligns with other global privacy frameworks, including:
UK GDPR
California Consumer Privacy Act (CCPA)
HIPAA
DIFC and ADGM data protection regulations
This regional approach supports organizations with strict data sovereignty and compliance requirements.
Cyber Essentials
Exclaimer is certified under the UK government-backed Cyber Essentials scheme, managed by the National Cyber Security Centre (NCSC). Cyber Essentials demonstrates that essential cyber hygiene practices are in place to protect systems from common internet-based threats.
This certification demonstrates a practical commitment to baseline security controls and threat resistance in cloud-hosted services.
Cloud Security Alliance (CSA)
Exclaimer’s cloud security controls are independently assessed under the Cloud Security Alliance (CSA) STAR program. This reinforces transparency around cloud security posture and aligns with industry expectations for secure SaaS offerings.
PCI DSS and payment security
Exclaimer is tested quarterly against PCI DSS requirements to validate secure handling of payment-related processes.
Exclaimer does not store credit or debit card details.
Payment transactions are handled separately via a PCI-compliant payment portal secured with high-grade SSL encryption.
This approach limits exposure and reduces the scope of sensitive data handled by the platform.
Continuous protection and monitoring
Security and data protection are embedded into Exclaimer’s operations, including:
Regular third-party penetration testing and vulnerability scanning
Internal security training for teams
Independent audits and compliance assessments
A demonstrated “A” rating on SecurityScorecard, reflecting a strong external security posture and low vulnerability risk.
What happens if Exclaimer experiences an outage?
The short answer is that email continues to flow. Exclaimer's designed so that a service disruption does not stop or block email delivery.
Reliability is critical for any system involved in email infrastructure. Exclaimer avoids single points of failure and handles faults transparently, without requiring action from IT teams or end users.
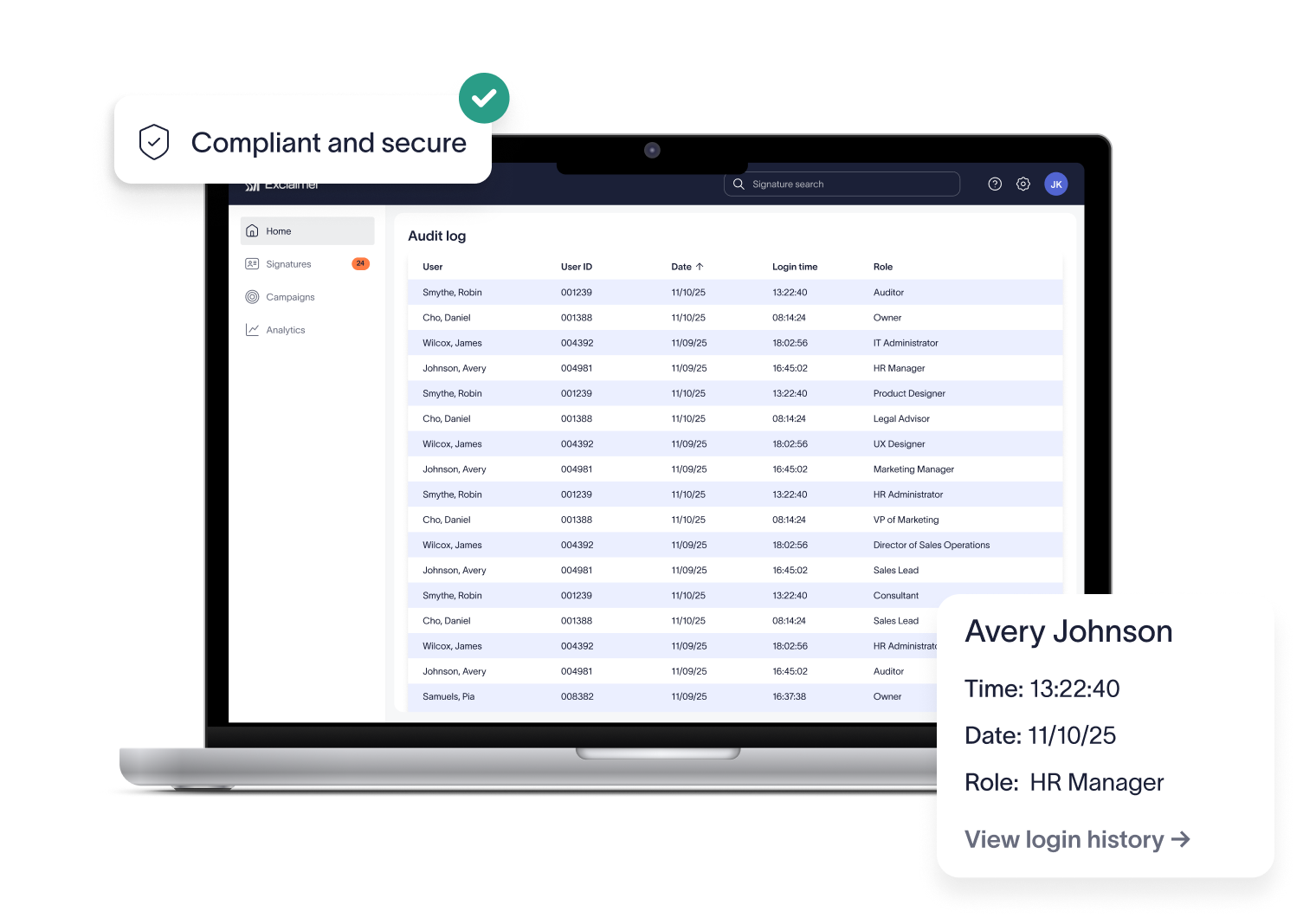
Continuous monitoring and automated response
Exclaimer’s service is monitored 24/7/365. Automated monitoring detects service alerts in real time and triggers predefined escalation chains. The primary objective of this monitoring is to maintain uninterrupted mail flow for all customers.
If an issue is detected at one regional datacenter, processing automatically shifts to the alternate location. Tenant data is continuously synchronized, so continuity is maintained without manual intervention.
Once the issue is resolved, the service continues operating as normal.
No impact on mail delivery
Exclaimer applies email signatures during message processing. However, it doesn't act as a mail transfer agent (MTA) and doesn't replace native Microsoft 365 or Google Workspace mail delivery.
This means:
Emails aren’t queued or blocked by Exclaimer
Mail continues to be delivered by the underlying email platform
Signature application resumes automatically when service is fully available
This prevents Exclaimer from becoming a single point of failure in email delivery.
Keeping pace with the Azure platform
Exclaimer’s development and QA teams continuously update the service to align with changes in Microsoft Azure.
All updates are built, tested, and validated before deployment, including stress testing beyond normal usage to prevent upstream issues.
How Exclaimer processes emails securely
Emails are processed in memory, encrypted in transit, and never stored permanently. When an email reaches the Exclaimer service, it's inspected only to determine whether a signature should be applied and where it should be placed.
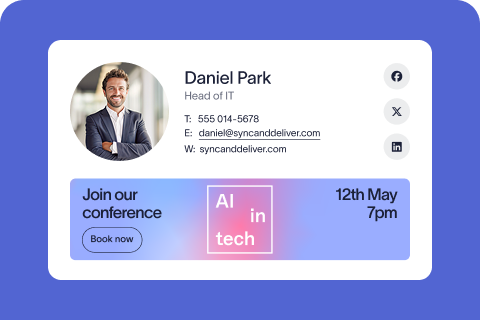
Message inspection and signature application
During processing, Exclaimer:
Checks the sender, recipient, and subject line
Determines whether a signature should be added or excluded
Decodes the message format (MIME or TNEF) to identify the correct placement
If an email is sent in Rich Text or Plain Text, it's converted to HTML so a complete HTML signature can be applied consistently.
Sender information is retrieved from cached directory data (Entra ID (Azure AD) or Google Directory), along with any approved custom attributes. These details are inserted into the assigned signature design, and the email is returned to the Microsoft 365 or Google Workspace tenant.
A unique certificate is used to authenticate correct tenant attribution during this process.
Encryption and data protection
All data in transit between Exclaimer and Microsoft 365 or Google Workspace is encrypted using RSA-2048-bit asymmetric encryption combined with a one-time AES (Rijndael) symmetric session key.
AES is the Advanced Encryption Standard selected by the U.S. National Institute of Standards and Technology (NIST) and is widely used to protect sensitive data in transit.
Encryption keys are issued and managed through certificates, with separate keys used specifically for encryption and decryption.
No permanent storage of email content
Exclaimer doesn't permanently store emails. Messages are processed in memory and encrypted at rest only for the time required to apply the signature.
For support and troubleshooting purposes, Exclaimer temporarily logs a minimal set of metadata for up to seven days:
Sender address
Recipient address
Applied signature ID
Message content, subject lines, and attachments aren't stored.
Encrypted messages and bypass behavior
If an email is already encrypted before reaching Exclaimer, such as with S/MIME, Microsoft OME, or IRM, the imprinting service can't modify it.
In these cases, the message bypasses signature processing and is delivered unchanged. Encryption and privacy are fully preserved.
Why reliability and security matter for IT teams evaluating Exclaimer
For IT teams, email signatures are part of how an organization controls outbound communications at scale.
Exclaimer is built to support that responsibility without adding risk. Reliability keeps mail flowing under all conditions. Governance applies branding, disclaimers, and identity under policy. Security keeps the service operating safely within Microsoft 365 or Google Workspace.
Just as important, Exclaimer has clear boundaries. It isn’t a threat-detection tool and doesn’t replace your existing security stack. Instead, it acts as a governed layer for standardizing email signatures without storing message content or becoming a delivery dependency.
For teams assessing vendor risk, this reduces exposure:
Email remains under your mail platform’s control
Signatures are managed centrally
Security practices are independently audited
That combination—reliability, policy control, and risk-aware design—makes Exclaimer trusted by enterprises that need scale without compromise.
See Exclaimer in action
Reading about reliability and security’s one thing. Seeing how Exclaimer works in your own environment’s another.
A free trial lets you evaluate how Exclaimer applies signatures, enforces policy, and operates within Microsoft 365 or Google Workspace—all without changing mail flow or committing upfront.
You can:
Deploy signatures in a test environment
Verify how data is handled and where it’s hosted
Confirm reliability, failover behavior, and visibility
Assess how Exclaimer fits into your existing governance model
Start a free trial to explore Exclaimer on your terms and see how centralized email signature management works at enterprise scale.