Role-based access control (RBAC) for centralized email signature management
28 October 2025
0 min read
TL;DR
- RBAC (role-based access control) assigns permissions to roles, not individuals—giving IT teams safer, more efficient control over email signature management
- It simplifies governance by allowing departments like Marketing, HR, and Legal to make approved updates without losing IT oversight
- Exclaimer extends RBAC across Microsoft 365 and Google Workspace, syncing user data and permissions automatically.
- Compliance and auditability are built in—every change is logged, creating a verifiable audit trail for ISO 27001, SOC 2, and GDPR frameworks.
- RBAC turns signature management into a scalable, secure process—reducing risk, saving time, and ensuring every email stays consistent and compliant.
Managing email signatures across an organization can be frustrating for IT teams. Between constant updates, marketing requests, and compliance requirements, even small changes can turn into hours of manual work. It’s a routine task that often creates unnecessary tickets and inconsistent results.
Role-based access control (RBAC) changes that. It’s a framework that assigns permissions to defined roles rather than individual users, so people only get access to what they need. In email signature management, RBAC lets IT delegate control safely, reduce workload, and keep complete oversight.
RBAC gives IT teams a structured, reliable way to manage email signatures at scale. It simplifies how access is granted, enforces consistency, and makes centralized management easier to maintain across the organization.
What is role-based access control (RBAC)?
As IT systems expand, managing access securely becomes harder. Giving every user unrestricted control increases the risk of errors, inconsistent data, and compliance breaches. Role-based access control (RBAC) provides a structured way to fix that.
 RBAC manages permissions by assigning access based on job roles rather than individuals. It follows the principle of least privilege defined by the National Institute of Standards and Technology (NIST)—granting only the access required to perform a task.
RBAC manages permissions by assigning access based on job roles rather than individuals. It follows the principle of least privilege defined by the National Institute of Standards and Technology (NIST)—granting only the access required to perform a task.
In practice, RBAC works like this:
Roles: Define grouped permissions, such as Admin, Editor, or Viewer.
Users: Are assigned to one or more roles depending on their responsibilities.
Policies: Control what each role can view, change, or approve.
This model reduces risk, improves compliance, and simplifies administration. It’s also easy to scale as roles stay consistent even as teams grow or reorganize.
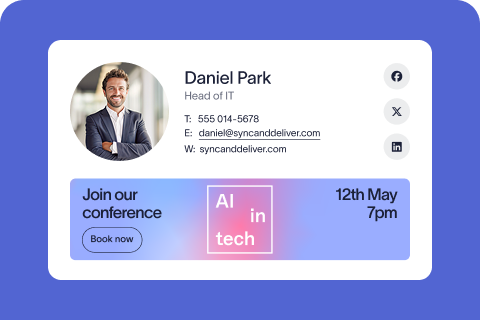
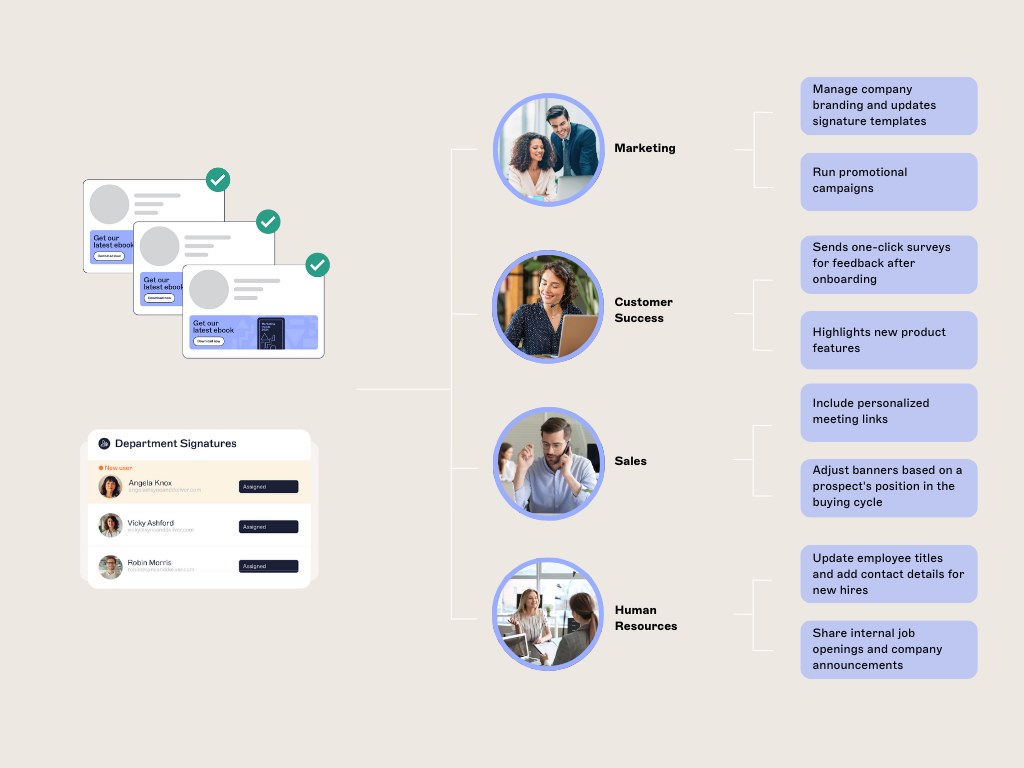
When applied to email signature management, RBAC creates clear boundaries between departments. Marketing can update email banners, HR can maintain staff details, and Legal can manage disclaimers. And all while IT keeps overall control.
Why IT teams need RBAC for email signature management
For most organizations, email signatures are a shared responsibility. However, it's IT that carries the burden of managing them. Each department wants something different. Without structure, small requests create backlogs and inconsistent results.
 RBAC solves this problem by giving IT precise control while allowing other teams to contribute safely.
RBAC solves this problem by giving IT precise control while allowing other teams to contribute safely.
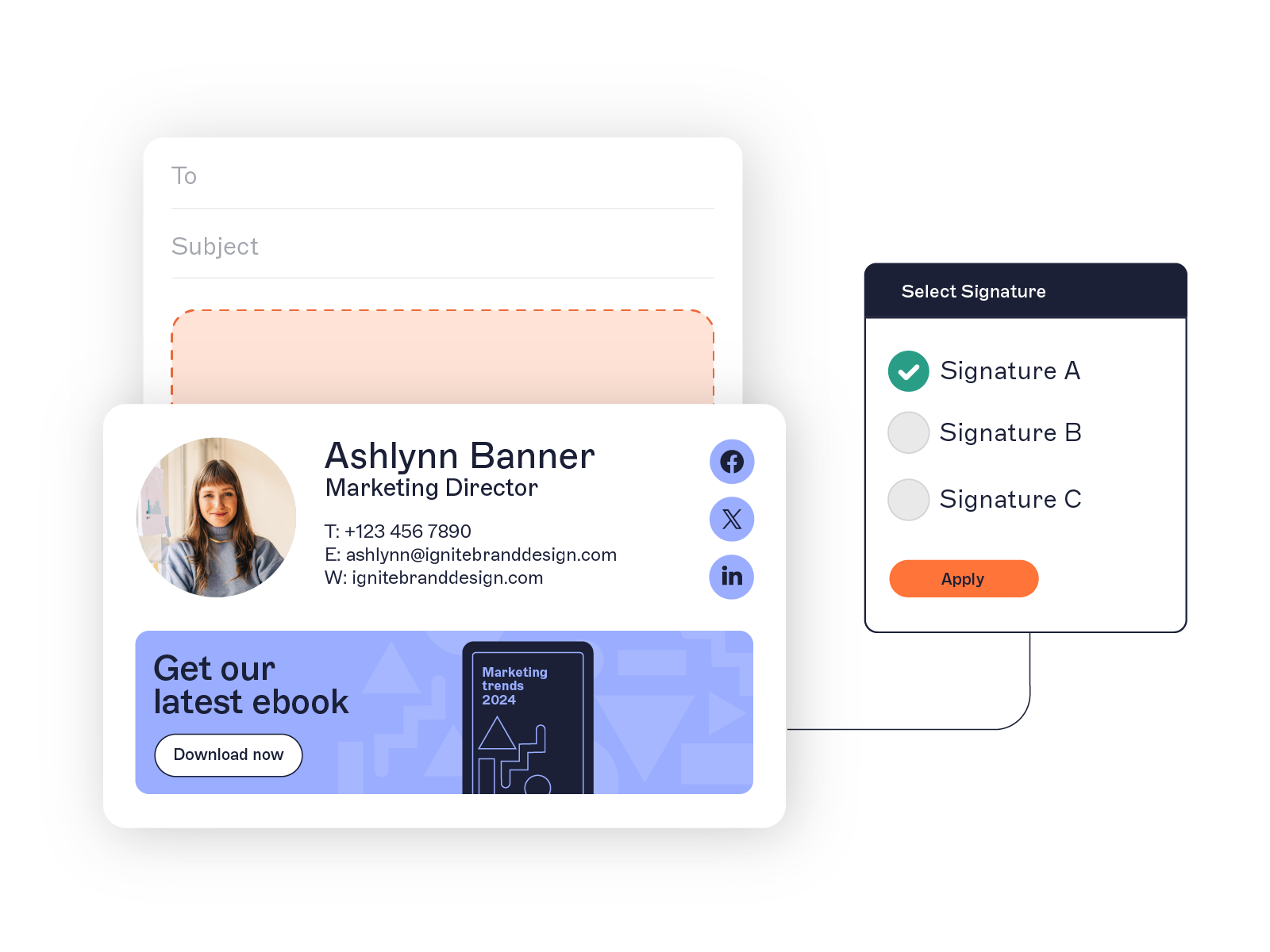
With role-based access control, IT can delegate permissions based on need:
Admins manage templates, policies, and deployments.
Editors update layouts, branding, or contact details.
Viewers review signatures for compliance or audit purposes.
This model perfectly aligns with how organizations already operate. In platforms like Microsoft 365 and Google Workspace, permissions are tied to roles, not individual users.
The benefits of RBAC for IT
Less manual work: Departments can make approved updates without creating IT tickets.
Built-in compliance: Disclaimers, branding, and formatting stay locked to prevent unauthorized edits.
Audit-ready control: Every change is tracked, creating a complete record for reviews or investigations.
Flexible delegation: Roles can be tailored by department, region, or business unit—no one-size-fits-all access.
RBAC transforms email signature management from a reactive support task into a structured, controlled process. IT remains the system owner, while other teams gain just enough access to stay productive.
How RBAC works in Microsoft 365 and Google Workspace
RBAC is already part of the core access model in both Microsoft 365 and Google Workspace. These platforms give IT teams a structured way to manage permissions and enforce least-privilege access across users and services.
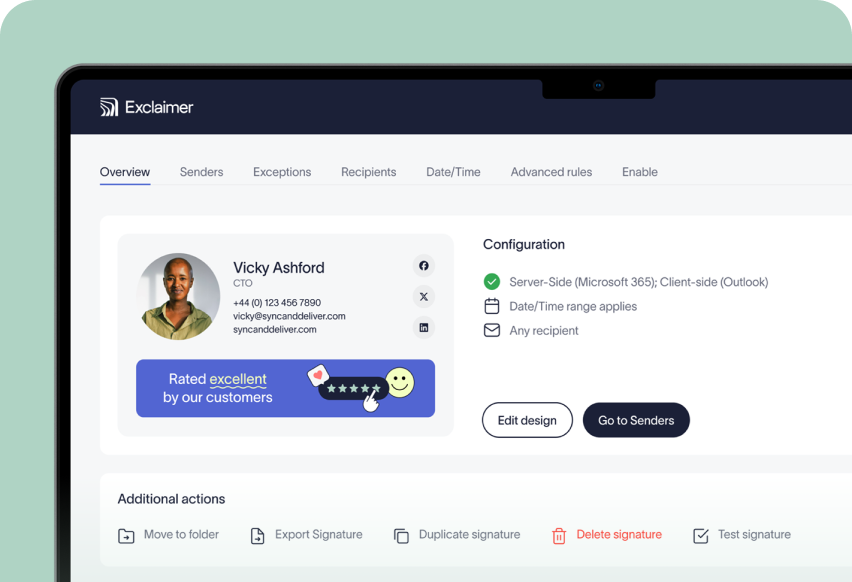
Exclaimer builds on that foundation, extending RBAC to email signature management for consistent governance across every email sent.
RBAC in Microsoft 365
In Microsoft 365, RBAC uses roles and role groups to control who can perform specific administrative tasks. Each role group includes a set of permissions tied to a defined scope. Some examples include managing mail flow, editing settings, or configuring policies.
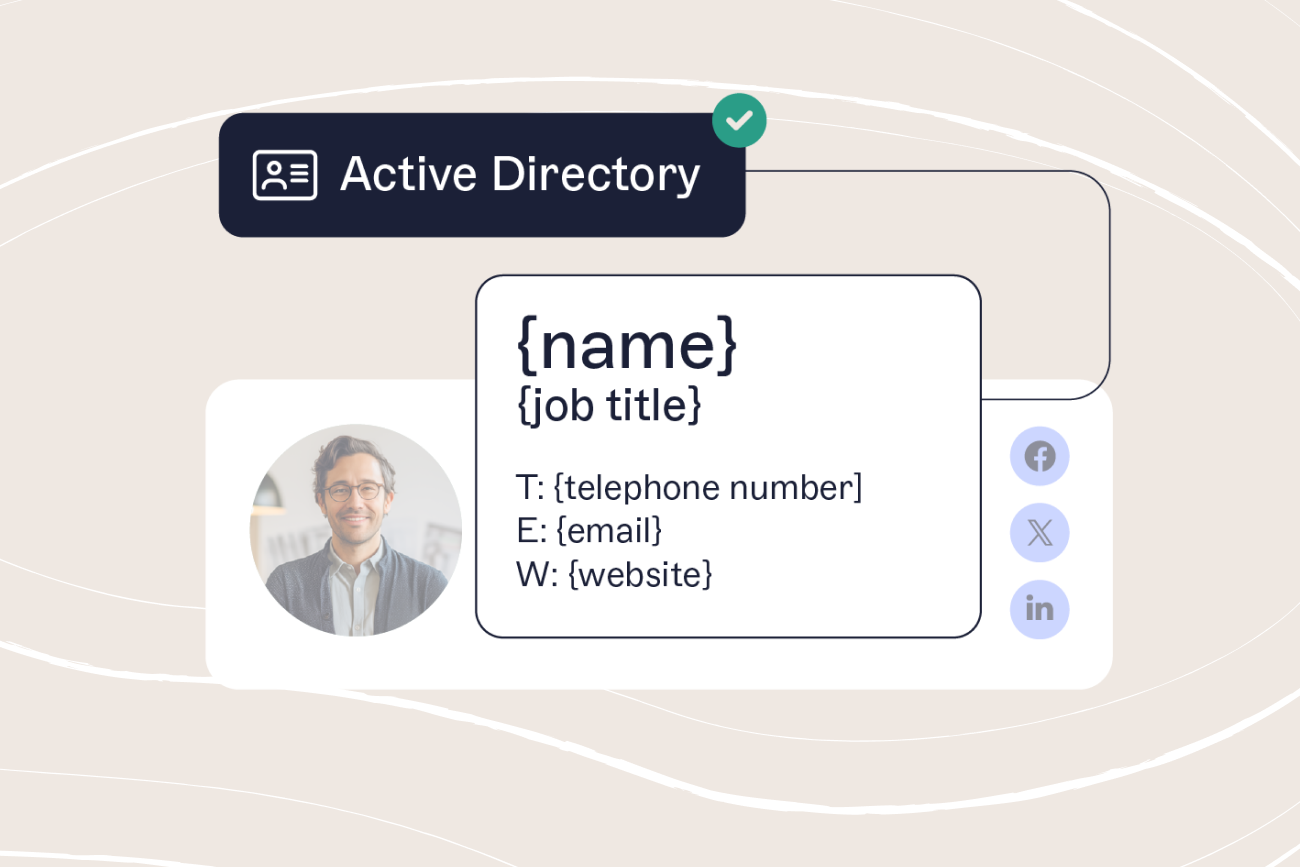
Exclaimer connects directly to Microsoft Entra ID (Azure Active Directory) to synchronize user data and permissions automatically. That means:
Admins can manage templates, policies, and organization-wide deployments.
Editors can adjust layouts, banners, or staff information within approved templates.
Viewers can audit signatures and verify compliance without making changes.
This structure aligns with Microsoft’s least-privilege access principle, minimizing the chance of accidental changes while keeping workflows efficient.
RBAC in Google Workspace
Google Workspace takes a similar approach, using predefined and custom roles to define access levels. Administrators can assign roles like Super Admin, Groups Admin, or create new ones tailored to their organizational needs.
Exclaimer integrates directly with Google Directory to extend these permissions into email signature management. Once connected, permissions and updates stay synchronized, so each department has the right level of control.
Design or marketing teams can manage signature visuals and banners.
HR can update staff data fields without editing template layouts.
IT maintains complete oversight across all accounts and departments.
Centralized control across platforms
By linking to your existing Microsoft 365 or Google Workspace directory, Exclaimer applies RBAC consistently across platforms. Any updates to user roles flow through automatically, keeping permissions aligned with your corporate directory.
This creates one policy, one source of truth, and one unified standard for email signature governance. All this reduces risk and removing the need for manual administration.
RBAC and compliance: Governance, auditability, and risk reduction
Compliance doesn’t stop at email security tools. Every message sent from your organization must meet regulatory, legal, and brand standards. That includes how disclaimers are applied, who controls them, and whether changes can be verified later.
RBAC helps IT teams meet these requirements by creating a structured, traceable access model for email signature management.
Governance through controlled access
With Exclaimer, permissions are defined at the role level. Only approved users can edit or publish email signature templates, and sensitive content—such as legal disclaimers or policy notices—can be restricted to authorized roles.
This reduces human error and helps organizations stay compliant with frameworks such as ISO 27001, SOC 2, and GDPR. By removing user-managed signatures, IT gains centralized control while still allowing departments to update content within defined boundaries.
Auditability and accountability
Every change made within Exclaimer is logged automatically. IT teams can see who made an update, when it was made, and what was changed. This audit trail provides verifiable proof of compliance and simplifies internal reviews or external audits.
Having this visibility also reduces time spent investigating discrepancies or unauthorized edits. This turns compliance from a reactive process into a reliable system.
Reducing operational and legal risk
Uncontrolled email signatures can expose organizations to brand inconsistency, outdated information, or even legal liability if required disclaimers are missing. RBAC prevents this by enforcing standardized permissions and locking down high-risk elements, such as legal text, logos, and contact details.
When every user operates within an approved role, IT can demonstrate that every outbound email meets company policy and regional regulations. The result is consistent, compliant communication that protects both your organization and its reputation.
Steps to implement RBAC in Exclaimer
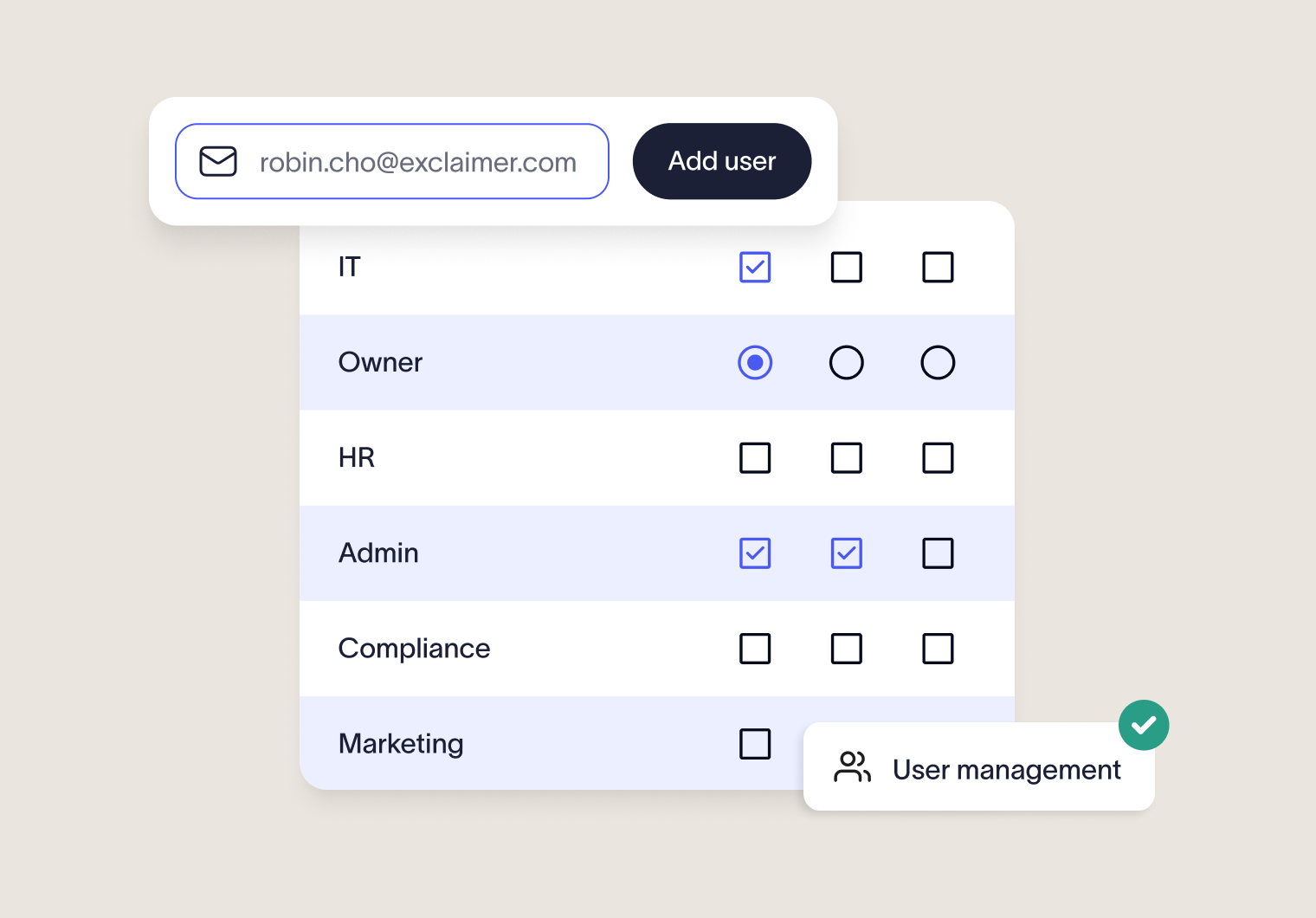
Setting up role-based access control (RBAC) in Exclaimer is straightforward. The process mirrors how permissions are managed in Microsoft 365 and Google Workspace, giving IT teams an easy way to apply the same governance model to email signature management.
1. Identify your core roles
Start by identifying who needs access and what kind of access they need.
Typical roles include:
Admins: Full control to create, edit, and deploy templates.
Editors: Can update layouts, banners, and employee details.
Viewers: Have read-only access for compliance reviews and audits.
This step sets the foundation for least-privilege access, giving everyone the right level of control.
2. Map responsibilities to permissions
Next, decide what each role can do. Keep access tied to responsibilities, and limit permissions wherever possible.
For example, Editors can update campaign banners, but only Admins should manage disclaimers or policy content.
3. Connect your directory
Integrate Exclaimer with Microsoft Entra ID or Google Directory. This syncs user data and role assignments automatically, creating a single, reliable source of truth for identity and permissions management.
4. Assign and review access
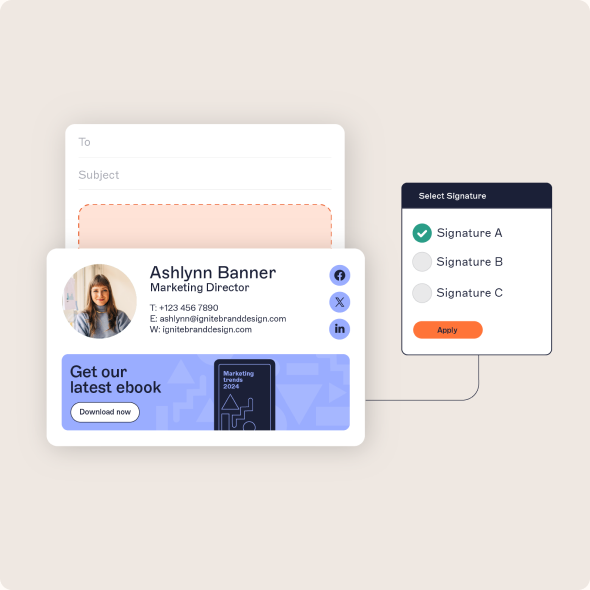
Use Exclaimer’s admin dashboard to assign roles. Review these assignments regularly to keep access up to date.
5. Test configurations
Before going live, confirm that permissions work as intended. Test user access across each role to verify that Editors can update templates, Viewers can audit, and Admins retain full control.
6. Monitor and audit regularly
Schedule regular reviews to confirm permissions still align with internal policies and compliance requirements. Exclaimer’s built-in change history logs every edit, timestamp, and user, making these reviews quick and reliable.
Tip: Document your RBAC policy and share it with IT and compliance teams. Clear records keep everyone aligned and make audits faster and easier.
Centralized email signature management made simple
RBAC brings structure and accountability to every part of email signature management. With Exclaimer's advanced feature set, that same control extends across your entire organization. It combines centralized oversight with safe, delegated access for different teams.
Exclaimer simplifies how IT manages permissions, keeps signatures consistent, and supports compliance goals.
 Here’s what that looks like in practice:
Here’s what that looks like in practice:
Consistent branding: Every email carries a standardized, professional signature that reflects your brand.
Delegated control: Marketing, HR, and Legal teams can update approved fields or banners without creating IT tickets.
Audit-ready visibility: Every change is recorded, providing a full history for compliance and governance reviews.
Directory synchronization: Permissions stay aligned automatically with Microsoft 365 or Google Workspace user roles.
This approach saves time, reduces compliance risk, and gives IT teams confidence that every outbound email is accurate, compliant, and on brand.
Exclaimer turns email signature management from a repetitive support task into a scalable governance process. One that's clear, controlled, and built for modern IT environments.